
“Companies everywhere are waking up to the reality that unmanaged data on personal smartphones is a huge security risk”
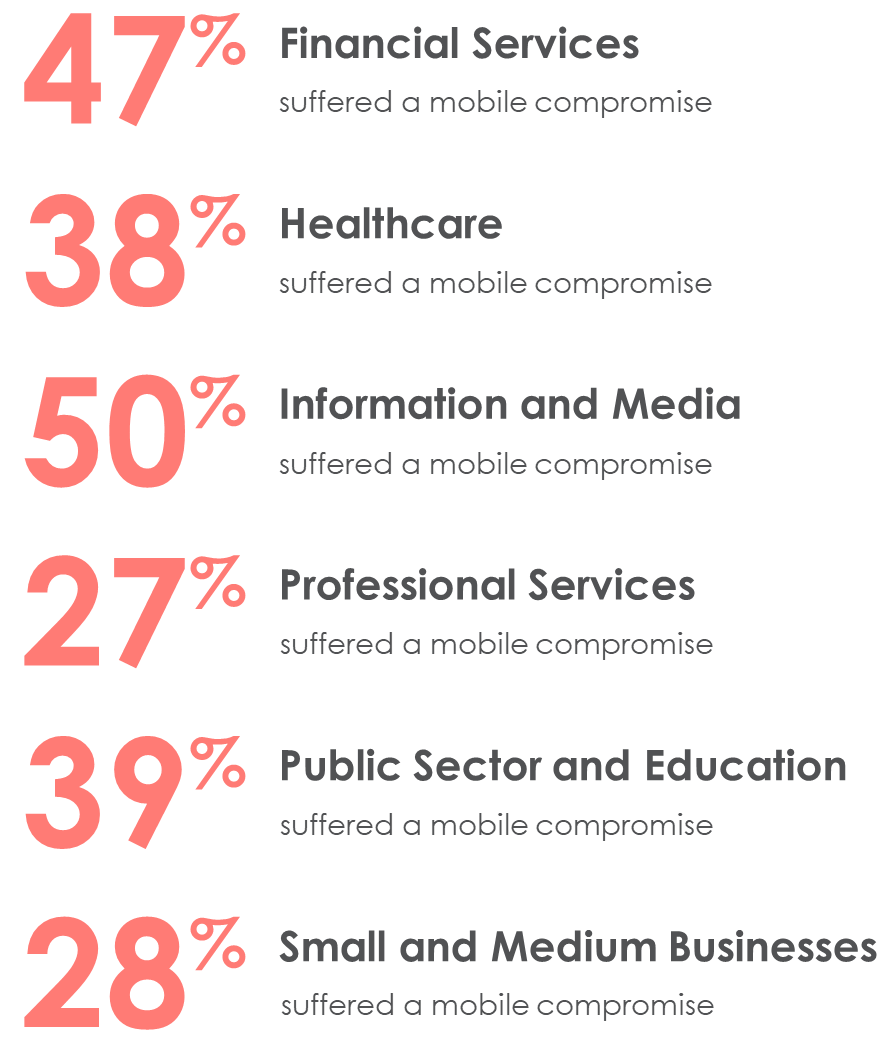
Ignoring mobile device security may come at your peril. Companies everywhere are waking up to the reality that unmanaged data on personal smartphones is a huge security risk. The Verizon Mobile Security Index 2020 Report has some shocking numbers.
Here’s the percentage of companies by industry that suffered a mobile breach in 2019.
Each has its own benefits, drawbacks, and considerations. Here’s a few of those you should know about as you consider protecting data on your employees’ smartphones.
Mobile Device Management
MDM is an established technology available to all modern mobile devices as well as Windows and macOS laptops. Vendors include Microsoft, VMWare, MobileIron, and Apple, amongst others.
MDM involves enrolling devices into the management solution of the company. This gives IT control of the device. With corporate devices it’s possible to have a device enrolled into an MDM when they are ordered. This provides the benefit of shipping a brand-new device directly to employees. Sweet!
But for personal devices, MDM can raise some questions from employees. Let’s go through a few challenges.
MDM is deemed as intrusive on personal devices
It comes as no surprise that many employees will bristle at the idea of handing control of their personal device to their company’s IT department. What employees may not realize is that this complaint is no longer factually accurate for personal devices if you don’t require full device enrollment.
Thanks to Android’s Work Profile and Apple’s User Enrollment, corporate profiles can be siloed and the operating system creates a separate logical partition from employees’ personal data and apps. The MDM technology cannot see the personal partition as it is encrypted with a separate encryption key.
For a good review of these new capabilities check out iOS User Enrollment for BYO Devices by Daniil Michine.
Many employees do not understand the nuances of these new capabilities, so if you choose to go with user enrollment and work profiles for personal devices, you will need to put a lot of effort into employee education.
Errant device wipes can cause major headaches
This applies if you elect to go with full device enrollment.
Some IT departments will create a policy in MDM to automatically wipe a device after a certain number of bad authorization attempts are entered. While this may seem like a good security feature initially, the result is that child of a distracted parent or colleague accidentally picking up the incorrect device may cause a device wipe.
Erasing personal photos and data is something a business should never do to an employee. It creates bad will and may impact your ability to retain your staff and hire top talent in the future.
If you elect for user enrollment / work profiles, then only the managed partition can be wiped, which removes the concern for this issue.
MDM Enrollment frustrates employees and eats help desk time
This issue tends to occur in a massive wave during the initial roll out. The story goes like this: IT spends months preparing, creates great how-to guides, sends multiple rounds of emails, holds voluntary lunch training sessions and all of which is holistically ignored by employees.
The day of the roll out, suddenly there’s a massive wave of confusion, frustration, and flat out refusal to enroll personal devices.
A smooth personal device MDM migration is an exception, not the norm.
Unfortunately, there is little difference in full device enrollment or a user enrollment / work profile implementation. Either way, the impetus is on the employee to perform the setup and some employees are going to need assistance – even if all the information in the word has been distributed prior to the roll out.
Mobile Application Management
In many situations, there is another viable option for protecting data on personal devices: mobile application management (MAM). MAM works in Microsoft Intune, which is included as part of the Microsoft 365 license suite. MAM does not require device enrollment and restricts IT control to only corporate data while still providing a wide range of security controls.
Employees will like that it doesn’t give IT control over their entire device, and IT will like that users adopt the program and corporate data is protected. We see it as a win-win, but it’s not a true magic bullet so let’s talk through some of the realities.
MAM is available on certain apps only
Mobile Application Management requires that certain functionality be built into the app executable itself. There is a list of supported Microsoft and partner applications here and the list is regularly updated.
This means that there are a limited number of mobile applications for which MAM is available. Depending on your industry and which line of business applications you use day to day, it may not be possible to leverage MAM.
However, the main concern for most businesses is email. Email can be protected in the Outlook app with MAM. And, you can protect attachments opened in Word, Excel, PowerPoint, and other Microsoft apps with MAM as well. This will suit most business use cases.
Note: If you are a developer or technical resource and want to know the underlying technology requirements, check out the documentation on the Intune SDK for Mobile.
Employees may be frustrated by enabled data protections
Protecting data inherently means restricting users’ freedoms with company data. The most common way this will surface is through restricting copy-and-paste operations for work data.
It is important to set expectations with employees with regards to MAM. Just because the device isn’t enrolled, doesn’t mean that there will not be some restricted behavior.
A very common gripe we see is the inability to copy an address from Outlook to Google Maps or Waze. MAM does not mean employees are free to do whatever they like with company data. It just means their personal apps, photos, documents, and information are not being managed and they don’t have to enroll their device.
Employees are responsible for installing apps
With MAM, there is no device enrollment. This means employees will need to download apps on their own – no company app store is provided. Employee’s get more control, but they also get more responsibility.
As a note, for Android devices, it is technically possible to setup apps in a company portal due to the underlying way the work profile is implemented in the operating system, but for iOS it is completely missing. As best practice we don’t recommend creating a bifurcated solution between device categories.
For a consistent employee experience, training material needs to point employees to the public app store for MAM solutions and employees need to be taught to install the applications they need.
Conclusion
It may be that MAM is not a viable solution for your business due to specific needs like line of business applications or the desire for an app store. However, we believe MAM is a viable solution for most businesses and results in better adoption in a BYOD environment, especially when email is the primary use case.
Ultimately, the most important way to secure data on personal devices is finding the right balance of privacy and security.
If you are interested in setting up a BYOD program for personal devices in your company, check out our BYOD 365 service or contact us.
Interested in a BYOD program for your business?
Our BYOD 365 service is designed to provide you with a formal BYOD policy document and guides you in creating a proper governance model so that you can succesfully implement a BYOD program that protects company data while respecting personal privacy.




