The increase in remote work over the past several years has caused an exodus from traditional methods of managing cloud apps in business endpoint ecosystems. In fact, as of 2022, 60% of all corporate data has been moved from on-prem storage to the cloud. The days of storing data on a file server protected behind firewalls are swiftly disappearing as most businesses shift to cloud-based management for hybrid workers.
The management of cloud apps within environments has become a primary concern for many IT administrators in recent years. In parallel with the rise of remote work has come a spike in shadow IT. Here, end-users are accessing and sharing data with unsanctioned and risky apps beyond the eyes of IT departments. Additionally, with third-party Software-as-a-Service (SaaS) applications, vulnerabilities outside the company environment can impact the security of user identities and company data.
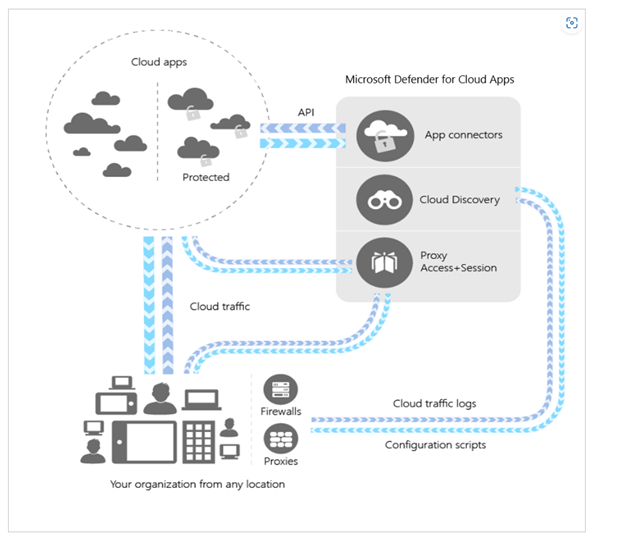
Microsoft Defender for Cloud Apps recognizes and addresses these challenges by allowing security experts to monitor and manage SaaS apps effectively. As a sophisticated Cloud Access Security Broker (CASB), it puts control back in administrators’ hands, overcoming shadow IT and vulnerabilities of third-party apps.

What is Microsoft Defender for Cloud Apps?
Defender for Cloud Apps is a modern CASB (Cloud Access Security Broker) meaning it is a security policy enforcement solution. CASBs are positioned between end-users and cloud service providers, often combining multiple security points. CASBs help IT administrators better understand their overall cloud posture across SaaS apps and cloud services.
Using a CASB such as Defender for Cloud Apps creates multiple security benefits including:
Shadow IT assessment and management
Achieved by delivering visibility into apps being used whether sanctioned or unsanctioned. Defender for Cloud Apps helps these processes with an app discovery process and continuous monitoring once discovered apps are identified.
Granular cloud usage control
Threat prevention via detection of unusual behavior, risky behavior, violations or suspicious data points in your cloud applications through policies.
Data Loss Prevention (DLP)
Policies enabled to prevent the unauthorized sharing of data.
Risk Visibility
The assessment of unsanctioned apps for possible risks is designed to make access decisions easier.
Threat Protection
The identification of High-risk application use and the subsequent remediation of threats.
Why are CASBs like Defender for Cloud Apps so Important?
CASBs are important as more and more companies expand the use of personal devices and 3rd party sites to access their network, and subsequently their data. They allow administrators to extend their security policies beyond the infrastructure of their own network and protect against threats from cloud applications. CASBs prevent data loss in the event of a breach and help to ensure regulatory compliance and data protection.
Use Cases for Defender for Cloud Apps and other CASBs
Discovery of all cloud apps and services being used
As Shadow IT runs rampant and leaves blind spots for many administrators, a CASB can deliver a 360-degree view of all cloud-based applications being used in your environment.
The Protection of data on unmanaged devices
According to the Endpoint Ecosystem study, 64% of workers are using a personal device for work, and only 43% of those devices have BYOD securely enabled. A CASBs ability to apply protection labels and prevent data downloads on unmanaged devices protects company data security at large.
Automating the Detection and Remediation of Malware in Cloud Apps
A CASB like Defender for Cloud Apps takes the element of human error out of the equation by automating remediation and detection of Malware. CASBs continuously monitor cloud-based apps and identify malicious files while offering automated remediation options when risky files are detected.
What Makes Defender for Cloud Apps Stand Out?
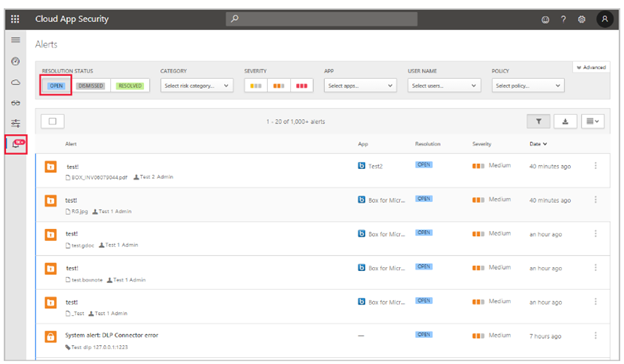 Source: Manage alerts – Microsoft Defender for Cloud Apps | Microsoft Learn
Source: Manage alerts – Microsoft Defender for Cloud Apps | Microsoft Learn
What does Microsoft Defender for Cloud Apps Do?
Detect App Vulnerabilities
The security posture of many businesses often largely depends on the adjoining security of cloud apps that are used within an environment. The Defender Cloud App Security component allows administrators to comb their environment easily and discover each app end users use that contains company data. The tool also gives a synopsis of security information on the app, making to decision to permit or terminate less complicated.
Protect Data Outside Your Environment
One of the major benefits of Defender Cloud Apps is the ability to build and host cloud apps safely. The tool allows you to fully manage and control not only the apps but also the APIs in your environment. This means, your business’ IT team is in full control of the cloud apps end users are using. Defender Cloud Apps allows your team to monitor, manage and derive operational insights easily within its dashboard.Perhaps most importantly, it allows your security team to see which cloud apps are being accessed, and sanction or unsanctioned their continued use in your environment. This enables administrators to secure all cloud apps in an environment while choosing to allow or eliminate connections based on predetermined security criteria.
Ease Administration in the Cloud App Security Portal
The features of Defender Cloud App Security are accessible within the tool’s portal. A unique and useful component the Defender Cloud App Security portal delivers is the ability to easily view each app connector working within your business environment, showing which third-party apps are active and the security posture of each one. The portal delivers security alerts when risky behavior is associated with the usage of third-party tools which allows admins to stay in the know and react swiftly if an incident occurs.Some additional information that is easily accessible within the portal include:
- A synopsis of at-risk identities
- IP addresses accessing your environment
- A summary of users and devices accessing your environment
- Compliance information for all cloud apps being used
- App-associated security alerts
- Active Policies
Additionally, Defender Cloud Apps allows security officials to view and monitor all events that take place within an app, while providing an ongoing summary of investigation priority (which tiers risky app-associated events that have occurred). For instance, if an access attempt occurs outside of a user’s typical behavior or location, the tool flags and documents the incident and then prioritizes the event’s review in the portal.This feature not only allows for simplicity in managing possible threats but creates in-depth intel for incident reports, which is critical when it comes to the ongoing improvement of a business’ security posture.
Create App-Based Event Policies
Natively, Defender Cloud App Security not only allows you to leverage all Microsoft’s default policies but also to create new policies derived from app-based events. These conditional access policies deliver more dynamic and fluid IT management processes and make detection-based response easily actionable.
Efficiency in Managing Cloud Apps
The reality today is that end-users will do everything in their power to be productive. This includes working outside of the box of IT teams’ expectations. In a hybrid work world, it often can feel like the wild west when it comes to monitoring and securing cloud apps connected to your business’ environment.Defender Cloud App Security makes managing and securing cloud apps efficient and attainable. As one of four key components of Microsoft Defender, App security is a necessity for any business operating with hybrid functionality.
What licenses include Defender for Cloud Apps?
Defender for Cloud Apps Integrates with Defender for Endpoint to help control shadow IT and eliminate threats. With the combined products, license holders can expect the following features to be delivered based on their selected plan:Microsoft 365 Business Premium licenses offer the following features for Defender for Cloud Apps:
- Automated Investigation and Response
- Endpoint Detection and Response
- Threat Analytics
- Vulnerability Management (core)
- Block at First Sight
- Enhanced ASR
- Tamper Protection
- Web Content Filtering
Microsoft E3 (A3 for education customers) license holders are offered the following features:
- The ability to access block at first sight
- Centralized Management
- Defender for Endpoint for Mac
- Defender for Endpoint for Mobile
- Enhanced ASR
- Manual Response Actions
- Tamper Protection
- Web Content Filtering
Microsoft E5 (A5 for education customers) license holders are offered the following features:
- Advanced Hunting
- Automated Investigation and Response
- Endpoint Detection and Response
- Evaluation Lab
- Access to Microsoft Threat Experts
- MIP Integration
- Threat Analytics
- Vulnerability Management
- Six months of data retention
Conclusion:
Microsoft Defender for Cloud Apps helps businesses provide strong security for sensitive data stored in cloud apps. It is an advanced CASB, that should be considered by businesses that take their cybersecurity initiatives seriously.Should you want to learn more about Defender for Cloud Apps or have questions about setting it up, the team here at Mobile Mentor will be happy to walk you through the details.

 Source:
Source: 


