
In today’s digital age, our identities are increasingly tied to our online presence. Protecting our digital identity is crucial to maintaining security and privacy in both personal and business contexts.
In the content below, we will explore the five essential steps of Identity and Access Management (IAM), commonly referred to as the 5 A’s: Authentication, Authorization, Administration, Analysis, and Auditing. By following these steps, you can take proactive measures to safeguard your digital identity and mitigate potential risks for your business.
Navigating the Endpoint Analytics Dashboard
Once you access the Endpoint Analytics dashboard, you’ll find a comprehensive overview of device performance, application reliability, and productivity metrics. The dashboard provides valuable insights into the overall health of the devices under management. While the specifics may vary depending on the configuration and baselines set, it generally offers information on startup performance, application reliability, and work-from-anywhere capabilities.
STARTUP PERFORMANCE: A MEASURE OF EFFICIENCY
Startup performance focuses on how swiftly devices boot up and become functional. Taking a critical look at startup performance, administrators can identify instances where devices take longer than expected to reach the desktop. This information can help troubleshoot issues such as resource-intensive startup applications that impede efficient boot times.
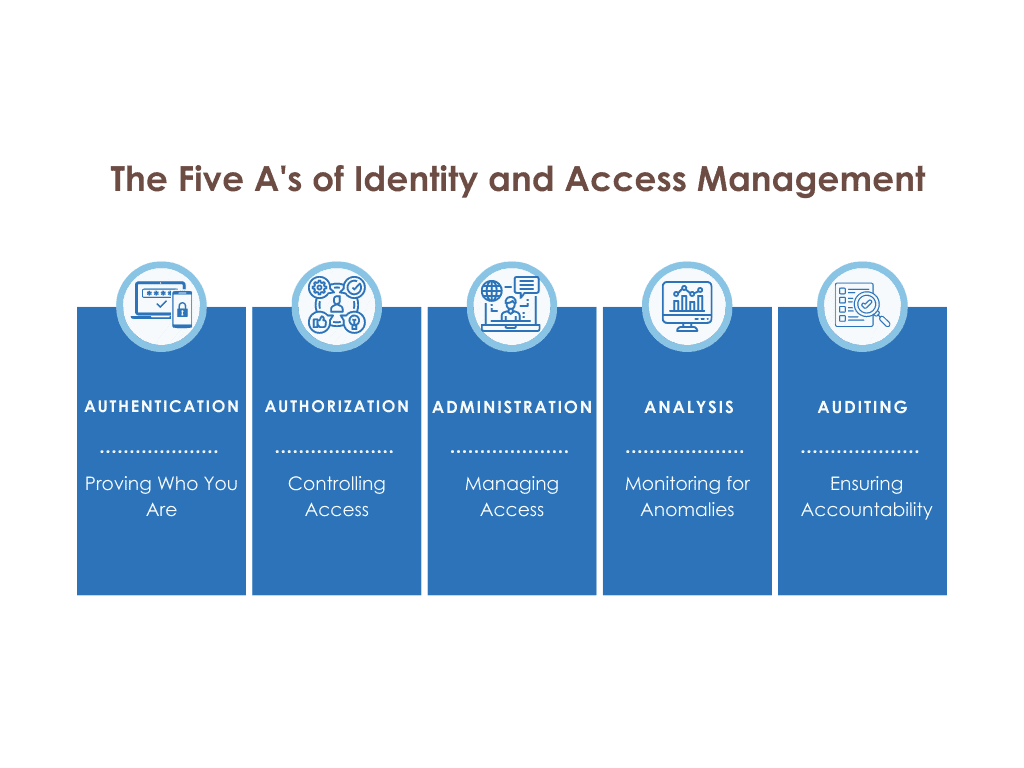
Step 1: Authentication – Proving Who You Are:
Authentication is the first layer of access to any digital environment. It involves verifying and proving that you are who you claim to be. Traditionally, this has been achieved through usernames and passwords. However, in the modern landscape, multi-factor authentication (MFA) has become increasingly important. By enabling MFA, you add an extra layer of security, requiring additional verification methods such as biometrics or one-time passwords. Implementing MFA correctly can significantly reduce the risk of unauthorized access and enhances the protection of your digital identity.
Step 2: Authorization – Controlling Access:
Once you have authenticated, authorization determines what resources and information you have access to within an environment. Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC) are commonly used methods to manage authorization. RBAC assigns permissions based on predefined roles, while ABAC considers specific attributes to grant access. To protect your digital identity, it is essential to review and regularly update your authorization settings, ensuring that access is granted only to the necessary resources and information.
Step 3: Administration – Managing Access:
Administration involves the tasks and processes required to manage access to resources. This can be centralized within an IT team or decentralized to individual resource owners. To enhance the health of your digital identity, consider implementing automated workflows for administration tasks. Automation streamlines access provisioning and deprovisioning, ensuring that employees’ access aligns with their roles and responsibilities. By automating these processes, you can minimize human error and reduce the risk of unauthorized access.
Step 4: Analysis – Monitoring for Anomalies:
Analysis focuses on monitoring and detecting unusual activities within your digital environment. By leveraging machine learning and artificial intelligence, you can identify potential security threats and unauthorized actions. Implementing sign-in risk or user risk policies allows you to apply conditional access policies and trigger reauthentication or reauthorization when suspicious behavior is detected. This proactive approach enhances the security of your digital identity and helps prevent unauthorized access.
Step 5: Auditing – Ensuring Accountability:
Auditing involves reviewing and assessing the access and entitlements of users within your digital environment. Regularly auditing your access controls helps identify any discrepancies, unauthorized access, or unused privileges. Access reviews enable you to remove unnecessary access rights and improve entitlements management. By maintaining a comprehensive audit trail, you ensure accountability and establish a robust foundation for the ongoing health of your digital identity.
Conclusion:
As our lives become increasingly intertwined with the digital realm, protecting our digital identity becomes paramount. By following the five steps of ensuring digital identity health – Authentication, Authorization, Administration, Analysis, and Auditing – you can ensure the ongoing health of your digital identity. Implementing multi-factor authentication, controlling access through RBAC and ABAC, automating administration tasks, monitoring for anomalies, and conducting regular audits are crucial practices to safeguard your digital identity. Prioritizing the security and protection of your digital identity empowers you to navigate the digital landscape with confidence and peace of mind.
Should you have any questions about ensuring the health of your digital identities or access management, feel free to drop us a line. We’ll be happy to help!
CONTACT US TO LEARN MORE ABOUT DIGITAL IDENTITY

Demetrius Cooper
Demetrius Cooper is Moblie Mentor’s Digital Identity lead. He has over 11 years of industry experience with a predominant focus on digital identity. A Chicago native, Demetrius lives and works in Atlanta, GA.



