
Securing Your Devices with Lookout for Work
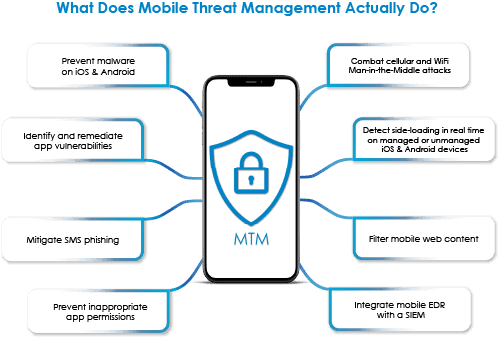
Lookout for Work is the leading MTM platform. The app provides persistent, on-device protection to combat the risks described above and it is effective on both Android and Apple devices. Mobile Mentor has been working with Lookout since 2016 and we love this tool.
How does Lookout Work?
The on-device Lookout for Work protection works by scanning apps that are installed on a device, checking certificates, and checking certificates of websites visited on the device. It does so without violating employee privacy by only checking certificates of websites against an internal database – and not spying on what device owners are viewing.
For those unfamiliar with Lookout, our team has developed a set of FAQs, found here to help businesses gain an understanding of the tool’s capabilities.
Conclusion:
In conclusion, the European Union’s Digital Markets Act (DMA) requiring Apple to allow side-loading of third-party apps has significant implications for iOS users and businesses with BYOD programs. This change may impact platform security, making Mobile Application Management (MAM) and Mobile Threat Management (MTM) crucial for safeguarding networks and data. Businesses should prepare by creating awareness, and understanding the differences between MDM, MAM and MTM. Most businesses will need to invest in a product like Lookout and Mobile Mentor is the ideal partner to deploy and manage this new capability. Embracing these changes responsibly will help businesses thrive in the evolving digital landscape under the DMA’s implementation.
CONTACT US TO LEARN MORE ABOUT LOOKOUT FOR WORK

Denis O’Shea
Denis founded Mobile Mentor in 2004 with a clear purpose – to empower people to achieve more with their technology. Technology is always changing but Denis’ purpose is the same and today most of Denis’s energy is helping clients to navigate the balance between security and employee experience.
Denis is really passionate about solutions that make an impact in healthcare, education and government. Since 2017, Denis has lived in the US, working with both public and private healthcare providers.



