We spend a lot of time assisting customers to realize the benefits and efficiencies of managing Windows 10 devices via the cloud by leveraging Microsoft Intune. We build out what we refer to as a ‘virtual image’, a similar concept to a legacy desktop image except it is dynamic, easily customised, easily deployed and easy to update remotely. We work to ensure that this build delivers a great user experience and meets the needs of the business.
At the completion of these projects, it’s clear that Modern Management is the best solution for the future management of devices, but this ultimately leads to a conversation about what options are available to get existing devices joined to Azure Active Directory (AAD) and fully managed out of the cloud?
This article talks about Azure AD joined devices and some of the options available to on-board your existing Windows 10 devices into Intune via Azure Active Directory.
What is an Azure AD joined device?
An Azure AD joined device is a company owned devices that requires an employee to sign-on to the device with their Azure AD identity. Once an employee authenticates with their Azure AD username and password they will be able to access the device, and any company resources deployed to the device. This approach is recommended for companies that:
-
Are providing or plan to provide cloud-based management of company owned devices via Intune.
-
Have employees accessing Microsoft 365 and other cloud services integrated with Azure AD.
-
Are moving away from on-premise domain joined services.
-
Have remote workers that have limited requirements to access on-premise infrastructure.
-
Are only using Azure AD rather than on-premise AD or are planning to move completely to Azure AD in the future.

What are the benefits of Azure AD joined devices?
Joining devices to Azure AD enables the following benefits
-
Single sign-on to cloud resources, which includes the Microsoft 365 suite of apps, SaaS applications and potentially on-premise applications.
-
Biometric authentication through Windows Hello for Business
-
Self-service password reset which is great for remote workers.
-
Full device management via Intune and zero-touch provisioning leveraging Windows Autopilot including automatic device license assignment.
-
Self-service enterprise application provisioning through the published enterprise app store.
-
Security benefits through leveraging device-based Conditional Access policies.
Options for onboarding existing Windows 10 devices
So now we understand some of the benefits of joining a device to Azure AD for modern management what are our options to get a device into this state?

Autopilot
Autopilot enables zero-touch provisioning of Windows 10 devices. New devices can be sent straight to employees with no pre-configuration required by IT.
Windows Autopilot sets up and pre-configures new devices from the cloud in a few steps. Once an employee can authenticate using their Azure AD identity, apps, profiles, and policies will automatically deploy over-the-air.
OEM ENABLED AUTOPILOT
For customers purchasing devices directly from an OEM, the OEM can automatically register the devices with Windows Autopilot once the organization has granted the OEM permission to do so. A list of supported OEM’s can be viewed via this link.
RESELLER ENABLED AUTOPILOT
For customers who purchase devices from a reseller, your reseller can add the Hardware ID’s of your devices to Autopilot at time of purchase. This means that the device can be sent directly to your employee from your reseller and be auto-provisioned when taken out of the box. A list of supported Resellers can be viewed via this link
MANUALLY ADD DEVICES TO AUTOPILOT
It is possible manually add the Hardware ID (Hardware Hash) of existing devices to Autopilot. This process is not very employee friendly and requires a factory reset of the device. This article talks through the steps on how to obtain the hardware ID to load into Autopilot.
IT or tech savvy employees would need to physically handle the device to obtain the Hardware ID and manually place devices into Autopilot.
As a work around we have seen customers opt for a swap out approach – sending a pre-provisioned Autopilot device to an employee, getting them to enrol into this device then send their existing device back to be reset and added to the swap-out pool. This is an effective approach if you have some spare hardware, time and employees who are not emotionally attached to their physical device.

Bulk Enrolment
It is possible to enrol Windows 10 devices to your Azure AD tenant using the Windows Configuration Designer app to build a provisioning package which can be applied to corporate owned devices to join them to your tenant and enrol them for Intune Management.
This option requires a local administrator to run the provisioning package if being applied to an already setup machine and the device must not be joined to a domain.
An Intune administrator will need to assign the Primary User for the device if it is not being used as a shared device once it has been joined to Azure AD and Intune.
Microsoft states this option is intended for new devices as any issues with the provisioning process may require a device wipe. You can read more about this process via this link.
Manually join devices to Azure AD
In some cases, we have customers that can’t factory reset their existing devices or where Autopilot is not a viable option. Factory resetting a device can provide a poor user experience or there may be a significant amount of local data stored on the device making a factory reset or a device swap out unacceptable.
For both Autopilot and manually joined devices, if you have Auto Enrollment enabled in Intune, devices will be automatically enrolled and marked as a company owned device without any additional user steps. Authentication to the Company Portal will be required as an additional set-up step if Auto Enrollment is not enabled.
MANUALLY JOIN AN EXISTING DEVICE
It is possible to un-join devices from the domain and then join them to Azure AD. This approach requires the employee to select Join this device to Azure Active Directory in Settings and to then sign into their Azure AD account. The join process must be started under an account that has Local Administrators permissions for the device.
Once the join has been completed the employee will be able to sign into the machine using their email address, but they will continue to have local administrator permissions for this device.
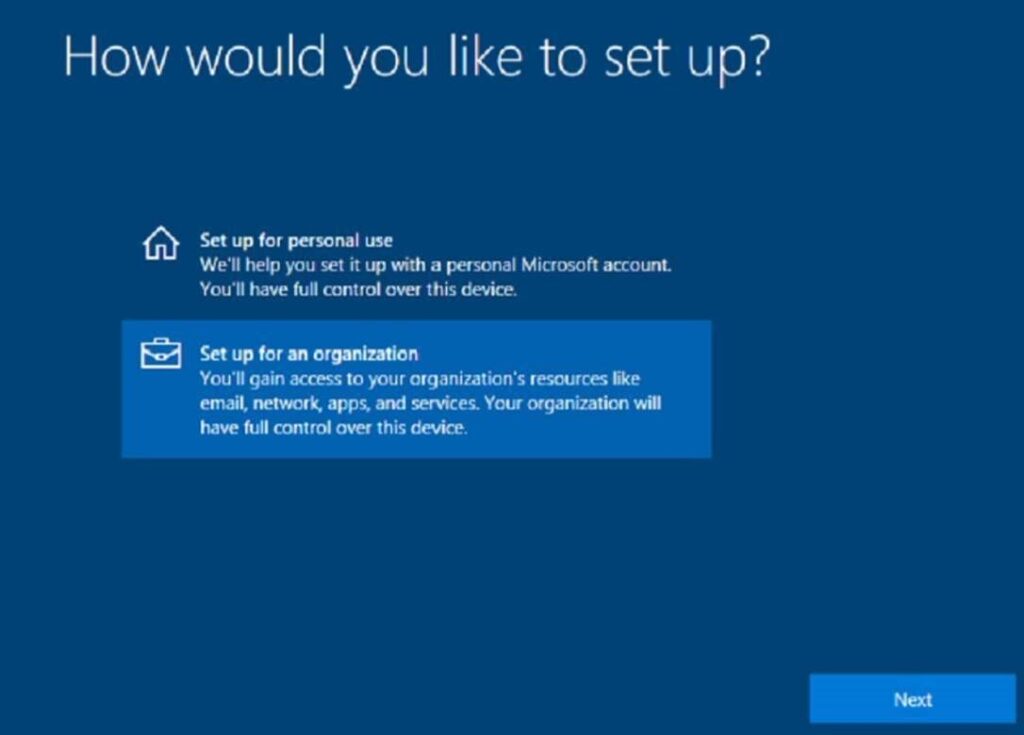
MANUALLY JOIN A NEW DEVICE
When setting up a device, during the Out of box experience (OOBE) there is an option to ‘set the device up for an organization’. At this screen, an employee can select this option and then authenticate using their Azure AD identity.
What about employee owned or BYOD devices?
Azure AD join is really only for devices that are company owned where the entire device is used for work and only one account is used on the device. With employee owned or contractor devices, they will be logging into their device with their own account or personal identity but will use their Azure AD identity to access company resources. For this scenario, Azure AD registration is used.
When a device is Azure AD registered, it is possible to ensure the device meets your compliance requirements before accessing company resources. You can still send security policies to these AAD registered devices (e.g require a passcode on the device) and will gain visibility of the device in your tenant.
REGISTERING THROUGH THE COMPANY PORTAL APP
Enrolling existing devices via the Company Portal app from the Microsoft Store is the easiest option for employees to Azure AD register their device. They can download the app and enrol using their Azure AD identity.
Be aware that if you are registering a device that has any existing policies and settings configured, these may conflict with Intune deployed policies and cause a poor user experience.
Not ready to go all in with Azure AD Join?
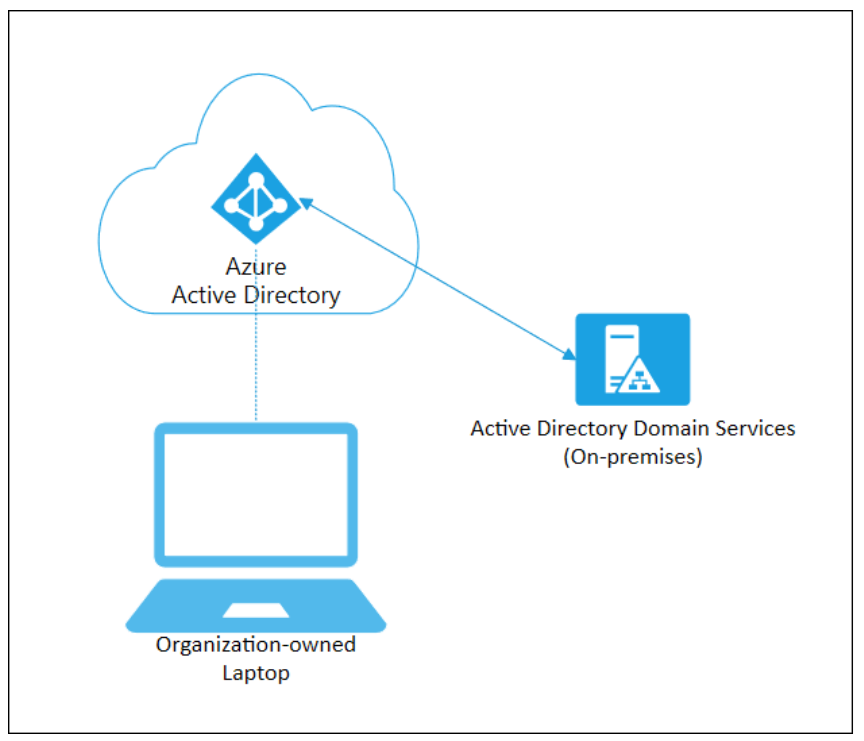
If you still have the need for devices to join to your on-premise domain and have apps deployed that require Active Directory authentication, you can leverage Hybrid Azure AD joined.
Hybrid Azure AD joined devices require line of sight to your Domain Controller which means you will likely need a VPN running on your devices for them to function remotely. This approach negates the benefits of a cloud solution and can deteriorate the user experience.
Rather than deploying Hybrid AD join, we recommend customers spend the time and effort cloud enabling their systems. This will provide a better user experience and improved management benefits in the long run.


Download the Six Pillars of Modern Endpoint Management
Deep Dive Concepts such as:
- Zero Trust
- Passwordless Authentication
- Zero Touch Provisioning
- App Management
- Over-The-Air Updates
- Remote Support