What is Microsoft Defender for Identity and how can it benefit your business?
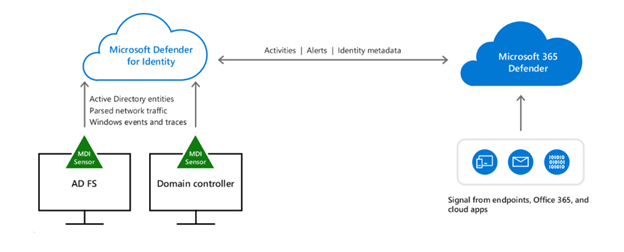
Defender for Identity is a security solution designed to protect against identity-based attacks in legacy Active Directory. Formerly known as Azure Advanced Threat Protection (Azure ATP), Defender for Identity extends Azure AD’s Zero Trust capabilities to on-premises domain controllers. It does so by protecting Active Directory accounts with behavioral-based monitoring.
The difference between Antivirus & Firewalls and Defender for Identity
Traditional security solutions such as firewalls and antivirus have proven ineffective when it comes to securing identities. This is because antiviruses are designed to protect against specific types of security threats, such as viruses, malware, and network attacks but don’t work to dissuade identity attacks like phishing scams and social engineering.
Identity-based attacks rely on compromised credentials on user accounts to gain access to an organization’s information. Defender for Identity works to prevent this by monitoring user accounts, entity behavior, and other malicious activities with learning-based analytics which detects advanced hacking attempts in a hybrid environment.
What makes Defender for Identity an advancement in Identity Security?
Defender for Identity uses advanced machine learning algorithms to detect and prevent identity-based attacks in real time. Microsoft uses its unparalleled volume of signals to feed its advanced machine learning in a way that surpasses competing programs. It analyzes user behavior and identifies anomalies that could indicate a potential security threat, such as login attempts from unusual locations or at unusual times. Furthermore, Defender for Identity uses risk-based conditional access policies to ensure that only authorized users are granted access to sensitive data and applications.
Another unique feature of Defender for Identity is its integration with Microsoft Azure Active Directory, allowing data and insights from Azure AD to provide comprehensive identity protection across an organization’s entire network. The integration streamlines the deployment and management of Defender for Identity, as it can be configured and monitored from within the Azure portal.
Some of the key benefits for businesses looking to leverage Defender for Identity include:
Investigation of alerts and user activities
Through the process of alert investigation, Defender for Identity detects suspicious activities on the network. Security teams can investigate these alerts using the Defender for Identity console, which provides details on the alert, including the user or entity involved, the type of activity detected, and the severity of the alert. The console provides guidance on how to respond to the alert, including recommended actions and next steps.
Protection from Lateral Movement
Defender for Identity protects against lateral movement using User Entity Behavioral Analytics (UEBA). By monitoring network traffic and identifying unusual activity, UEBA can detect lateral movement and other suspicious behavior. It also offers threat intelligence via authentication monitoring and the enforcement of strong authentication policies, which further prevent lateral movement. Defender for Identity allows security teams to investigate user activity on the network, including logins, failed logins, and other authentication activities.
Reconnaissance
Reconnaissance refers to the process of gathering information about a target or a potential target with the aim of identifying vulnerabilities that could be exploited by attackers.
In the case of possible attackers, reconnaissance may involve collecting information about individuals or groups that may be interested in attacking a particular system or organization. This information can include:
-
Motivations: Understanding the motives behind a potential attack can help security professionals anticipate the types of attacks that may be launched and identify the targets that may be most vulnerable.
-
Tools and techniques: Attackers may use a variety of tools and techniques to launch their attacks. Knowing what these are can help security professionals identify and prevent attacks before they occur.
-
Weaknesses: Reconnaissance can also help identify weaknesses in an organization’s defenses, such as vulnerabilities in software, network configurations, or physical security.
-
Patterns: By analyzing past attacks or suspicious activities, security professionals can identify patterns of behavior that may indicate an impending attack.
Identification of Compromised Credentials
Compromised credential alerts help teams to identify and remediate issues. Compromised credentials can lead to unauthorized access to sensitive information and systems. If an attacker gains access to a user’s credentials, they can impersonate that user and access their accounts or sensitive data without raising any suspicion. This can have serious consequences, such as data breaches, financial fraud, and even identity theft. Moreover, attackers can use compromised credentials to launch more sophisticated attacks, such as phishing, spear-phishing, and social engineering attacks. By proactively identifying compromised credentials, IT teams are able to remediate threats and their consequences.
Automated Response
A component that IT professionals find particularly useful for identity protection is Defender for Identity’s Automated Response. This feature automatically takes action to quarantine or remove threats without any input from the user. The ability to automatically respond to detected threats reduces the need for manual intervention and also speeds up response time.
Domain Dominance Detection
This component of Defender for Identity flags attack methods such as Remote code execution, malicious replication, service creation, skeleton key, and golden ticket. By identifying the domains that are most active on the network, administrators can allocate their resources more effectively. They can focus on securing the most active domains first, thereby reducing their overall risk.
Components of Defender for Identity:
-
Advanced Threat Protection
Advanced AI and machine learning is used to detect and respond to advanced threats in real-time, including threats that target identities and credentials.
-
Integrated Security
Defender for Identity is integrated with other Microsoft security products, such as Azure Active Directory, which helps to provide a comprehensive security solution for businesses.
-
Compliance
Defender for Identity provides comprehensive auditing and reporting capabilities which lends a hand to IT groups striving to meet compliance requirements.
-
Security Recommendations
Defender for Identity automated security recommendations are provided to help teams prioritize initiatives and harden their environment.
Microsoft Defender for Identity License Requirements
Microsoft Defender for Identity is available as a standalone subscription or as part of certain Microsoft licensing packages. Here are the Microsoft licenses that include Microsoft Defender for Identity and what they include:
Microsoft 365 E5/A5:
This license includes Microsoft Defender for Identity, in addition to other security and compliance features such as Microsoft Defender for Endpoint, Microsoft Cloud App Security, and Azure Information Protection.
Microsoft 365 E5/A5 Security:
This license includes only security features such as Microsoft Defender for Identity, Microsoft Defender for Endpoint, Azure Advanced Threat Protection, and Azure AD Premium Plan 2.
Microsoft Defender for Identity standalone subscription:
This is a standalone subscription that includes only Microsoft Defender for Identity.
It’s worth noting that the specific features and capabilities included in each license may vary depending on the version of the license and the subscription level.
Conclusion
Microsoft Defender for Identity helps businesses secure their digital identities and effectively protect against social engineering threats. It is a sophisticated tool that should be considered by businesses that take the protection of digital identities seriously.
If you want to learn more about Defender for Identity or have questions about setting it up, the team here at Mobile Mentor will be happy to walk you through the details.

Andrew Reade
Andrew is our Digital Marketing Manager and oversees web-based marketing strategies and content creation for the organization. As a marketing veteran, Andrew has worked with organizations of all sizes in a diverse group of industries, from Risk Management to Transportation. Joining the organization in 2021, Andrew is based in Mobile Mentor’s Nashville, TN office.




