
“You can now leverage your Azure Active Directory identities to enrol Apple devices”
You can now leverage your Azure Active Directory identities to enrol Apple devices
Apple released iOS BYOD User Enrolment and Shared iPads last year. Both these solutions leverage a managed Apple ID to establish a user identity on the device for secure access to company apps and data.
Managed Apple IDs
-
Are owned and managed by an organisation
-
Provide employees access to certain company specific Apple services
-
Are created automatically using federated authentication
-
Can also be used to assign roles within Apple Business Manager
Managed Apple IDs are unique to your company and separate from personal Apple IDs that employees create for themselves.
Managed Apple IDs have less access on a device than a personal Apple ID. Find My, Sidecar, Apple Pay, iCloud mail and family sharing are some of the options not available when using a Managed Apple ID.
Administrators can restrict access to and remove Managed Apple ID accounts via Apple Business Manager.
Azure Active Directory Federation
Managed Apple IDs are delivered through a federation between Apple Business Manager and Azure Active Directory.
This federation unlocks to opportunity to
-
Have a single identity across all your employees’ devices
-
Use a single identity to enrol an Apple BYOD or Shared iPad device
-
Have Single Sign-on for the Microsoft Apps for Enterprise on iOS devices e.g. Outlook and Teams on iPhone and iPad.
Federation Requirements
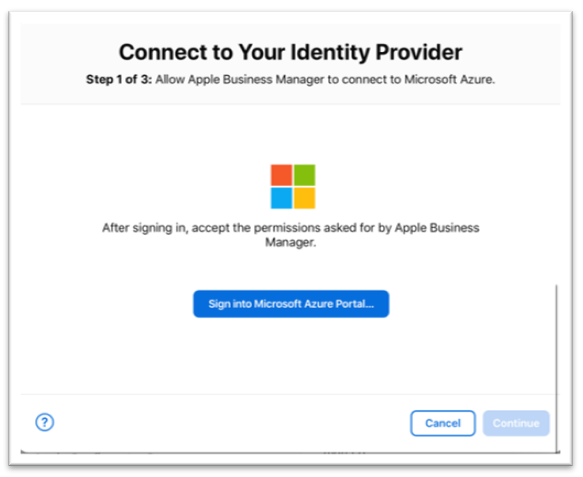
From the Apple Business Manager console, you can initiate the federation with Microsoft Azure Active Directory (AAD) to automatically create Managed Apple IDs that match to your company identity.
Federated authentication requires that users’ UserPrincipalName match their email address. UserPrincipalName aliases are not supported.
Also, Apple devices leveraging Managed Apple IDs must meet the following minimum requirements
-
iOS 11.3 or later
-
iPadOS 13.1 or later
-
macOS 10.13.4 or later
Federation Process
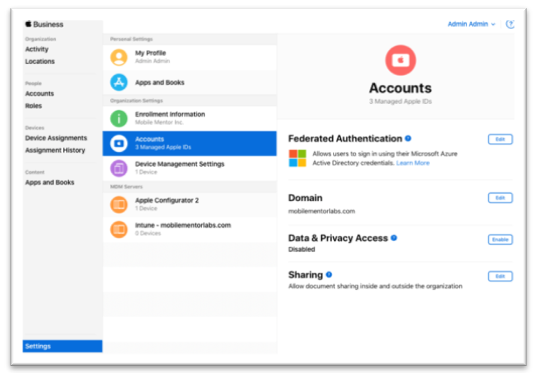
Federation Authentication configuration is located in Apple Business Manger under Settings > Accounts
Note: You will need to have an administrator account in Azure Active Directory that has sufficient rights to allow the connection between Apple Business Manager and Azure Active Directory.
Personal Apple IDs
The federation between ABM and AAD is a bit tricky as it needs each employee’s company email address only to be associated for this managed Apple ID and not any other Apple ID.
If an employee has used their company email address to create an Apple ID in the past for accessing the App Store, iCloud, or other Apple services such as an Apple Developers account then they will need to change this Apple ID to use a different email address.
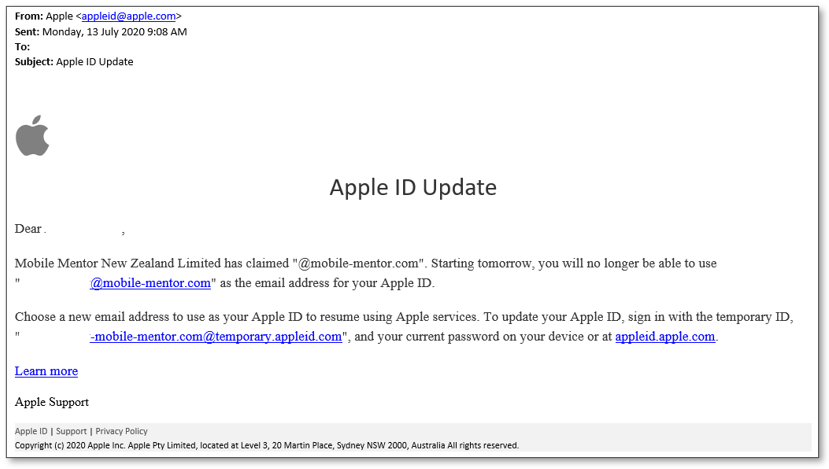
Once the federation process is initiated, they will have 60 days to change their Apple ID to use another email other than their company email address.
After 60 days, their Apple ID will automatically be renamed to a temporary username and the original username is released and claimed by the company.
Apple documents these steps via this article https://support.apple.com/en-us/HT202667
An example of the email from Apple that your employees will receive during this process is shown below
Conclusion
If you are looking to enable Shared iPads or User Enrollment for iOS devices we recommend you get started on the federation process now. The process to move personal Apple IDs off your company email domain will take 60 days and until that process is complete you will not be able to move forward.
If you would like to learn more about this, contact us.
If you’re interested in learning how iOS devices could work in your business, check our Intune Security Baseline service, or BYOD 365.
Learn More about Intune for Windows




